Update: NIST has released the draft now. Please see here for news on the latest NIST 800 Rev 3 Draft.
The National Institute of Standards and Technology (NIST) that is a part of the US Department of Commerce has invited public comments to update the existing NIST Guide to Industrial Control Systems (ICS) Security, SP 800-82 Rev 2 to SP 800-82 (Rev 3).
The deadline for comments is May 28, 2021. An Initial Public Draft of the update, which will be published as SP 800-82 Rev. 3, is scheduled for a late 2021/early 2022 release.
The original document was published in the year 2015 and the threat landscape as well as what we refer to as Industrial Control Systems have changed drastically.
What new stuff should be included in SP 800-82?
NIST is aware of changes to the threat landscape regarding ICS security and also about what really can be considered as an Industrial Control System. and therefore are in the process of updating this guide. They have invited public comments for the update. If you are connected with ICS Security in any way whether as a Industrial Control System user, vendor, system integrator or security researcher who is concerned with ICS security, then you have an opportunity to make your voice heard.
Specifically NIST wants your inputs on the following aspects:
-
-
Expansion in scope of SP 800-82.
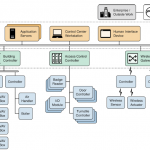
Whether an expansion in the scope from industrial control systems to control systems in general is needed, because SP 800-82 has been used in areas outside the scope of what we refer to as Industrial Control Systems. Similar systems are used everywhere from Building Automation Systems to Air Traffic Control Systems and these systems being similar to ICS are also vulnerable to the same threats as do their industrial cousins based on DCS, PLC or SCADA systems.
-
Application of new cybersecurity capabilities in control system environments.
The proposed update seeks to provide guidance on new capabilities such as anomaly detection and new technologies such as the Internet of Things (IoT), Machine Learning, Digital Twins and so on. This is not included in the current document, but will be included in the new update.
-
Development of guidance specific to small and medium-sized control system owners and operators.
There is a need for more guidance to help small and medium-sized control system owners and operators to have tools and techniques that better fit their needs. A small industrial facility using a couple of PLCs and an HMI cannot invest in something like a patch server or an Intrusion Detection System. However they are vulnerable to cyber threats that can affect their small control systems adversely.
-
Updates to control system threats, vulnerabilities, standards, and recommended practices.
This is sorely needed. NIST wants to know how they can provide this on an ongoing basis. We at Abhisam had published this as one of our ICS Security Trends 2021 and we are glad to know that something would be done regarding this.
-
Updates to the control system Overlay.
The proposed update would revise the control system Overlay to align with SP 800-53, Rev. 5 and SP 800-53B, and take care of the change in scope to control systems in general.
-
Removal of material from the current document.
This refers to obsolete material or practices that are no longer applicable. This is important so that users of the document can focus their energies on what needs to be actually done for Industrial Control Systems Security, rather than what is being done merely to comply with obsolete recommendations.
-
Of course, all comments and suggestions must be specific and backed by logic, or prior incidents in the ICS Security field, or current best practices in ICS security that can result in making these systems more secure, or relevant recommendations from other industry standards such as IEC 62443 or the NERC CIP Standards for Power Plants or similar.
Where can I learn more about ICS Security?
Abhisam has an excellent self paced online learning course on ICS Security training course here that is modular and comes with its own certification on passing the exam.
Do you have any other information regarding SCADA Cyber Security?
You can read more about SCADA cyber security here.